The transportation sector has traditionally been spared by attackers. However, this is no longer the case.

What has changed?
First, the number of active attackers continues to increase. Cybercrime has become an attractive criminal profession. The low risk of being caught and the high profitability of virtual attacks are among the factors that attract criminals. We therefore need to understand that there are more attackers than ever before, and naturally they have a much greater strike force.
The number of vulnerable organizations is also growing at an unprecedented rate. Many companies that are not fundamentally technology-based are now forced to set up interconnected systems, opening up gateways for cybercriminals. As if that were not enough, the multiplication of exploitable vulnerabilities in software and connected hardware increases the fragility of the companies that roll them out.
Thus, we are witnessing a perfect storm: there are more attackers, there are more potential victims, and the latter are rolling out technologies that increasingly expose them.
There are so many attackers that they need to specialize and hone their skills in particular areas and develop in-depth expertise. Some cybercriminals specialize in obtaining and reselling VPN access from compromised companies, making it possible to buy VPN accounts from a “pre-compromised” company for as little as $100.
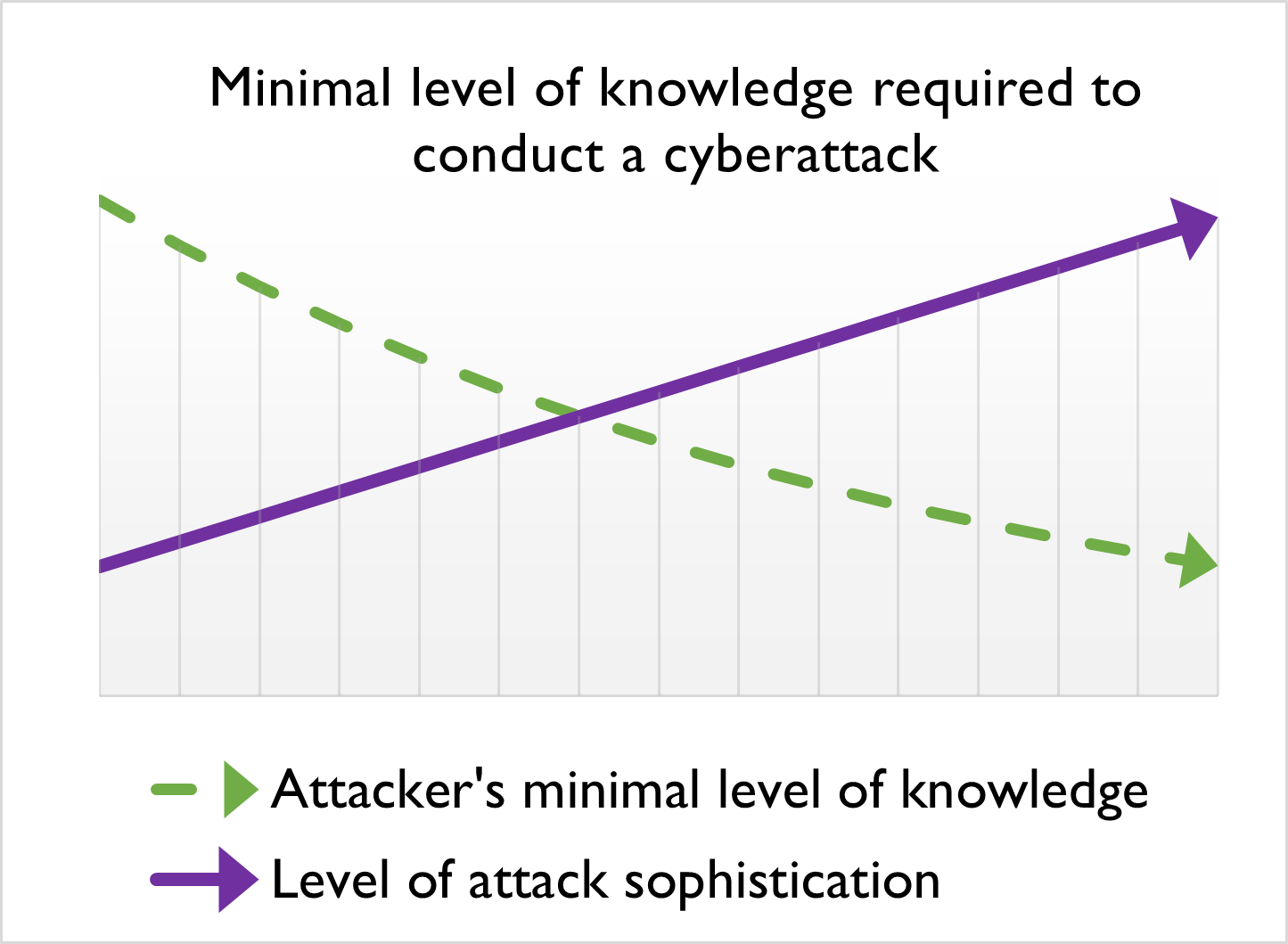
Other attackers specialize in the discovery and resale of vulnerabilities. Criminals have created a whole “crime-as-a-service” economy, enabling them to connect with other attackers interested in their services. Thanks to this ecosystem, a cyber attack draws on the specializations of several distinct attackers, resulting in a much more sophisticated cyberattack, which is perpetrated by several attackers operating like a well-honed production line. In practice, we notice that cyberattacks are becoming increasingly sophisticated, while the level of knowledge required to perpetrate them is decreasing.
This sophistication comes at the same time as a type of cyberattack that has revolutionized all cybercrime: ransomware. Based on the principle of extortion, this attack aims to exfiltrate sensitive information and causing downtime for the victim organization, failing to pay a ransom. Ransomware has been extremely profitable in recent years, but more importantly, it has proven effective against all types of businesses, from not-for-profit organizations (NPOs) to companies operating in critical sectors.
Of course, the transportation sector is hit particularly hard by this scourge.
The challenge of securing data
The overall transportation sector faces several challenges, the first one being protecting the huge amount of data it produces and consumes.

Data is at the heart of major innovations in this sector. Transportation systems use sensors, connected objects, mobile applications and artificial intelligence to enhance passenger experience, and optimize routes and schedules. Traffic management systems use sensors and cameras to collect data on traffic conditions in real time, and use it to optimize routes, regulate traffic lights and reduce congestion. Autonomous vehicles (cars, trains, subway trains) transport passengers and goods based exclusively on data and sensors.
Special attention must be given to protecting this data, notably to safeguard its availability and integrity. Unlike other industries, where protecting confidentiality is the main issue, the transportation sector must above all protect the availability and integrity of data, any breach of which would have catastrophic impacts.
Data is difficult to protect because it must be monitored and protected in several places: in the source system, in transit and then in the destination system. Data is considered as secure as the weakest link.
The challenge of securing OT networks
The second challenge in the transportation sector is that operational environments often include legacy elements that were designed at a time when cybersecurity was not a consideration. This is particularly true of industrial systems and connected objects. All their cybersecurity relied on the logical or physical segregation of these systems, but the convergence of IT and OT systems is quietly removing this barrier for attackers. These systems, which often control public safety, are therefore increasingly exposed to cyberattacks.
To protect these systems, we need to secure their perimeters and maintain increased surveillance at every interconnection point. We also need to intensify our efforts, meticulously analyzing every change and integration to ensure that it does not provide an opening for an attacker. Apart from planned evolutions and changes, vulnerability audits should be conducted periodically to ensure that the infrastructure is not inadvertently exposed. If you do not perform these audits, attackers will do it for you.
The challenge of cybersecurity workforce
The third challenge is the lack of cybersecurity specialists to support organizations in securing their operations. However, this lack of resources is not unique to the transportation sector. While it is advisable to call upon outside help to carry out more specialized analyses, such as vulnerability audits and intrusion tests, it remains critical to have trained in-house staff ensuring day-to-day cybersecurity and keeping abreast of the latest developments in this area.
CIMA+ specializes in cybersecurity in the transportation industry. We can help you protect your data and systems from cyber threats. Feel free to contact us.
Unity is strength
Attackers have realized that they need to work together. In the same way, the transportation industry needs to unite to better defend itself. A number of resources are available to achieve this.
In Canada, Public Safety offers the “Regional Resilience Assessment Program (RRAP)”, which includes a resilience assessment and vulnerability audit for owners and operators of critical infrastructure facilities. You can take advantage of this program via the Public Safety portal: https://www.publicsafety.gc.ca/cnt/ntnl-scrt/crtcl-nfrstrctr/crtcl-nfrstrtr-rrap-en.aspx.
Another thing to do is to consume the material provided by the ISAC covering your sub-sector. ISACs (Information Sharing and Analysis Centres) are North American non-profit organizations that act as a one-stop shop delivering information on sector-specific cyber threats. They disseminate cybersecurity newsletters from public safety agencies and specialized firms, and provide their members with appropriate training and awareness material. ISACs also function as neutral entities, enabling members to anonymously share their experience of cyberattacks, and to pass on the lessons learned from these attacks.
Three ISACs are available in the transportation sector:
- Surface Transportation ISAC (ST-ISAC)
- Over The Road Bus ISAC (OTRB-ISAC)
- Public Transportation ISAC (PT-ISAC)

Membership is open to all organizations working in the sector, and is available via the portal: https://surfacetransportationisac.org/.
In addition, in the United States, the TSA has developed the “Surface Transportation Cybersecurity Toolkit", which is a portal centralizing educational material ranging from awareness-raising material, sector-specific cybersecurity considerations, to special bulletins published by the U.S. Department of Homeland Security (DHS).
In short, the transportation sector is rapidly innovating, and increasingly exposed to cyberattacks. But it is also a suitable time to integrate cybersecurity into your projects, from the earliest stages.
Including cybersecurity considerations from the outset of your projects represents the biggest advantage you will have over attackers.
Cybersecurity challenges are common to all companies in the sector, and we need to use the lessons learned from our peers and cybersecurity specialists working in our field to better integrate cybersecurity principles. In cybersecurity, unity is strength!
To access the original article and read the full magazine (French only), visit the AQTr website here: https://aqtr.com/association/bibliotheque/revue-routes-transport-edition-printemps-2023-repenser-securite-demain